December this year is full of surprises. Microsoft has decided to close this year with a zero-day vulnerability in Windows kernel and 38 other vulnerabilities.
Adobe however was far more optimistic to address 87 vulnerabilities just in Adobe Reader and Acrobat. Last week Adobe also issued an out-of-bound update for Adobe Flash Player, closing 2 vulnerabilities, including 1 zero-day.
Let’s have a close look at all of these vulnerabilities.
Microsoft
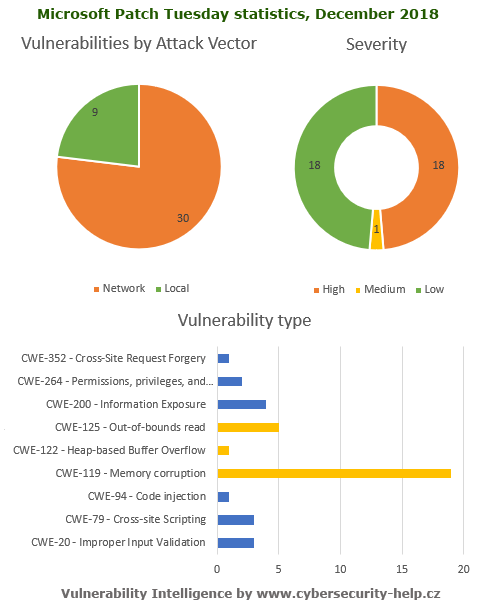
Microsoft patched 39 vulnerabilities. Among them one 0day vulnerability in Windows kernel (CVE-2018-8611). The vulnerability allows a local user to execute arbitrary code on the system with elevated privileges. So far there is no public information about the attack itself. We know only that Microsoft credited Kaspersky Lab for discovery of this issue.
The majority of fixed vulnerabilities are as usual buffer management related errors, as shown below.
Adobe
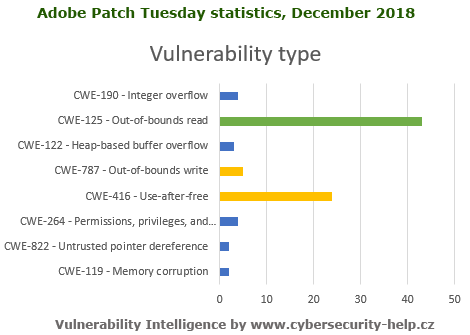
With Adobe situation is not better. All fixed vulnerabilities are remotely exploitable. 36 vulnerabilities were assigned High security risk, 51 vulnerabilities are considered low-risk errors.
Distribution of vulnerabilities in Adobe Reader and Acrobat is shown below:
Below is a table with the list of all vulnerabilities patched by Microsoft.
Table #1. Vulnerabilities fixed by Microsoft
| Software | Severity | CVE/CVSS | Known exploits |
| SB2018121125: XSS in Microsoft SharePoint Server (1) | |||
| Microsoft SharePoint Server | Low |
CVE-2018-8650 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121124: Privilege escalation in Visual Studio in Microsoft Windows (1) | |||
| Visual Studio | Low |
CVE-2018-8599 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121123: Privilege escalation in Diagnostics Hub Standard Collector Service (1) | |||
|
Windows Windows Server |
Low |
CVE-2018-8599 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121122: Denial of service in Connected User Experiences and Telemetry Service (1) | |||
|
Windows Server Windows |
Low |
CVE-2018-8612 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121121: Information disclosure in Remote Procedure Call runtime in Microsoft Windows (1) | |||
|
Windows Windows Server |
Low |
CVE-2018-8514 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121120: Remote code execution in Microsoft Text-To-Speech (1) | |||
|
Windows Windows Server |
High |
CVE-2018-8634 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121119: Remote code execution in Microsoft PowerPoint (1) | |||
|
Microsoft Office for Mac Microsoft PowerPoint Microsoft Office Compatibility Pack Microsoft SharePoint Server Microsoft Office Web Apps Office Online Server Microsoft Office |
High |
CVE-2018-8628 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121118: Remote code execution in Microsoft Chakracore (5) | |||
| ChakraCore | High |
CVE-2018-8629 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8624 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8618 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8617 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8583 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121117: Remote code execution in Microsoft Outlook (1) | |||
|
Microsoft Outlook Microsoft Office |
High |
CVE-2018-8587 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121116: Security restrictions bypass in Microsoft Exchange Server (1) | |||
| Microsoft Exchange Server | Low |
CVE-2018-8604 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121115: Information disclosure in Microsoft Windows GDI (2) | |||
|
Windows Windows Server |
Low |
CVE-2018-8596 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8595 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121114: Multiple vulnerabilities in Microsoft Excel (4) | |||
|
Microsoft Excel Microsoft Office Microsoft Office for Mac Microsoft Office Compatibility Pack Excel Services on Microsoft SharePoint Server |
High |
CVE-2018-8636 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8627 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8598 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8597 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121113: Multiple vulnerabilities in Microsoft .NET Framework (2) | |||
| Microsoft .NET Framework | High |
CVE-2018-8540 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8517 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:P/RL:O/RC:C |
Public exploit code for vulnerability #2 is available. |
| SB2018121112: Information disclosure in Microsoft DirectX (1) | |||
|
Windows Windows Server |
Low |
CVE-2018-8638 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121111: Multiple vulnerabilities in Microsoft Windows kernel (7) | |||
|
Windows Windows Server |
Low |
CVE-2018-8649 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:N/I:N/A:H/E:U/RL:O/RC:C CVE-2018-8641 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8639 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8637 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8622 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8621 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8477 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121110: Remote code execution in Microosft Windows DNS Server (1) | |||
|
Windows Server Windows |
High |
CVE-2018-8626 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121109: XSS in Microsoft Dynamics NAV (1) | |||
| Dynamics NAV | Low |
CVE-2018-8651 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121108: Cross-site scripting in Microsoft Azure (1) | |||
| Windows Azure Pack | Low |
CVE-2018-8652 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018121107: Remote code execution in Microsoft Internet Explorer (4) | |||
| Microsoft Internet Explorer | High |
CVE-2018-8643 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8631 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8619 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8625 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121106: Remote code execution in Microsoft Edge (5) | |||
| Microsoft Edge | High |
CVE-2018-8629 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8624 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8618 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8617 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8583 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018121105: Privilege escalation in Windows kernel (1) | |||
|
Windows Windows Server |
Medium |
CVE-2018-8611 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:H/RL:O/RC:C |
This vulnerability is being exploited in the wild. |
| SB2018121104: Multiple vulnerabilities in Microsoft SharePoint (2) | |||
| Microsoft SharePoint Server | High |
CVE-2018-8635 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8580 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
Table #2. Vulnerabilities fixed by Adobe
| Software | Severity | CVE/CVSS | Known exploits |
| SB2018121103: Multiple vulnerabilities in Adobe Reader and Acrobat (87) | |||
|
Adobe Acrobat DC Adobe Acrobat Reader DC |
High |
CVE-2018-15998 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15987 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16004 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19720 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16045 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16044 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16018 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19715 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19713 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19708 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19707 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19700 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19698 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16046 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16040 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16039 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16037 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16036 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16029 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16027 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16026 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16025 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16014 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16011 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16008 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16003 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15994 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15993 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15992 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15991 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15990 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19702 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16016 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16000 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15999 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-15988 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19716 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-16021 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-12830 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-19717 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19714 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19712 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19711 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19710 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19709 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19706 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19705 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19704 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19703 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19701 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19699 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16047 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16043 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16041 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16038 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16035 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16034 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16033 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16032 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16031 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16030 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16028 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16024 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16023 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16022 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16020 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16019 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16017 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16015 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16013 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16012 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16010 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16006 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16005 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16002 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16001 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-15997 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-15996 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-15989 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-15985 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-15984 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-19719 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16009 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16007 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-15995 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-15986 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-16042 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |