Vulnerability Management Platform
Our vulnerability management platform stands as your vigilant guardian, detecting, prioritizing, and helping you remediate potential threats before they get exploited by hackers.
Start for free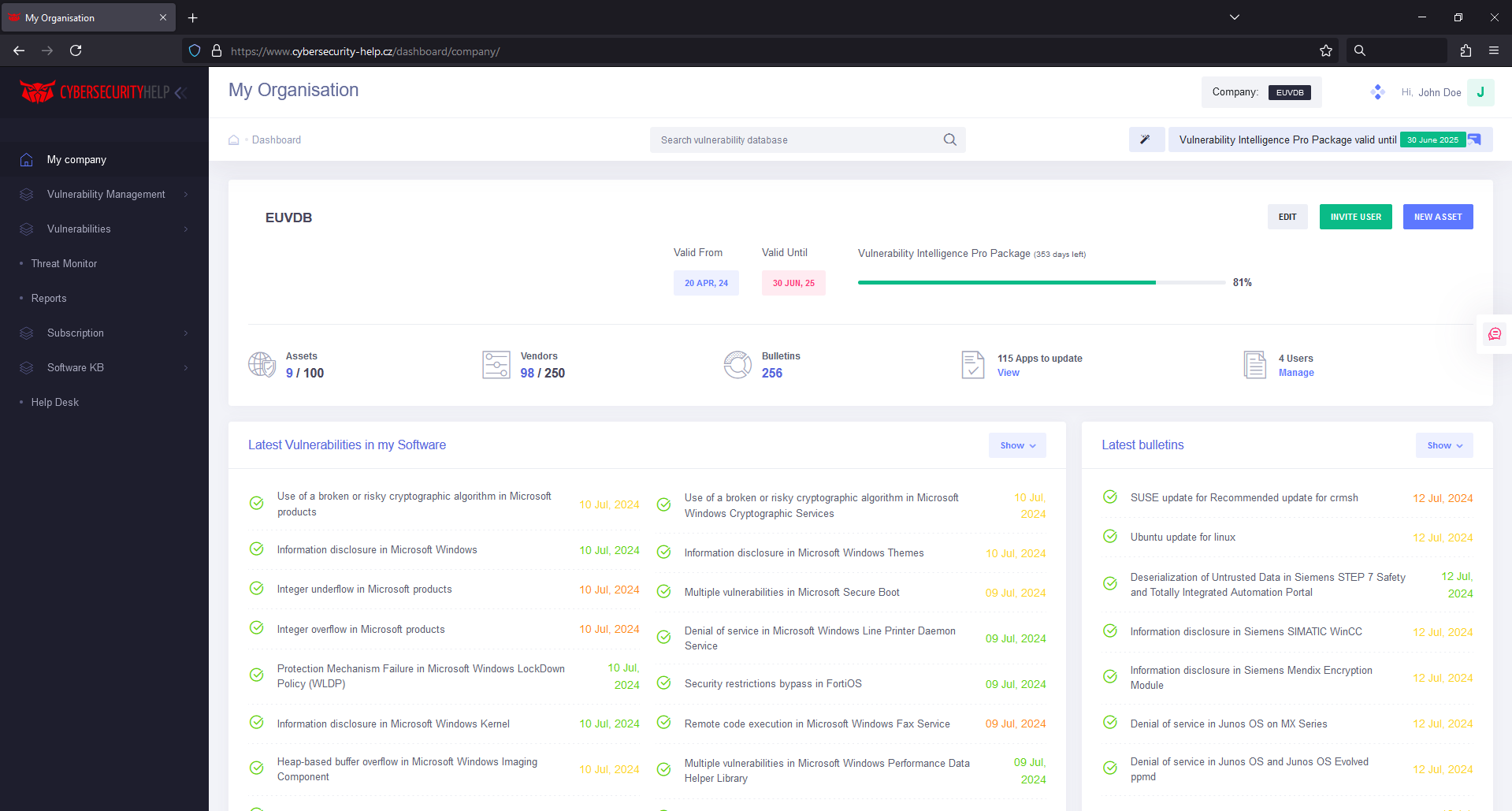

Vulnerability scanner
CSH Agent is a vulnerability scanner tool that can be deployed on desktop and server systems to continuously monitor your company’s assets and instantly notify you on the ongoing or potential threats.
Vulnerability Management by Cybersecurity Help offers:

Comprehensive Risk Assessment
Uncover vulnerabilities across your entire network using both agent and agentless approaches.

Intelligent Prioritization
It is important to understand, which vulnerabilities have to be addressed ASAP so that your company stays secure and your IT department can plan and execute their tasks in time.

Actionable Insights
Our intuitive dashboard delivers real-time data on new vulnerabilities, exploits and zero-days, empowering you to make informed decisions and swiftly mitigate threats.

Continuous Monitoring
We monitor security state of your systems 24/7 even if they are offline at the moment. There is no need to wait for the scan results anymore to see if your systems are vulnerable to a particular threat.
Vulnerability Management
Vulnerability statistics
Vulnerability Intelligence
Vulnerability management platform uses our database of knwon vulnerabilities to provide actionable and personalized vulnerability intelligence.
View Vulnerability Database

How does this work?
Software that can be downloaded from our website and deployed across your desktops and servers
You can manually create assets and assign software to them without the need to install any agents. This way you will be able to receive alerts on the latest threats. Such approach will work with various routers, switches and other hardware that usually cannot be monitored using the classical agent approach as well as for regular desktops and servers.
If you already have a vulnerability management solution, you can simply connect it to our dashboard using API to enrich your current solution with our vulnerability intelligence.

Protect your system from threats
Our vulnerability management platform stands as your vigilant guardian, detecting, prioritizing, and helping you remediate potential threats before they got exploited by hackers.