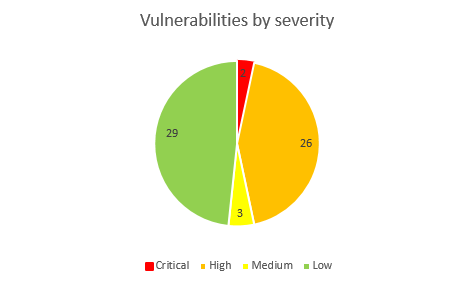
Today Microsoft has released security fixes for 60 vulnerabilities in total. Among them 2 zero-days in Windows Shell (CVE-2018-8414) and Internet Explorer (CVE-2018-8373) rated as Critical by our analysts, 26 vulnerabilities have high severity rating, 3 – medium, and 29 are rated low.
43 vulnerabilities can be exploited remotely, 16 locally and one vulnerability in Cortana requires physical access to the affected device.
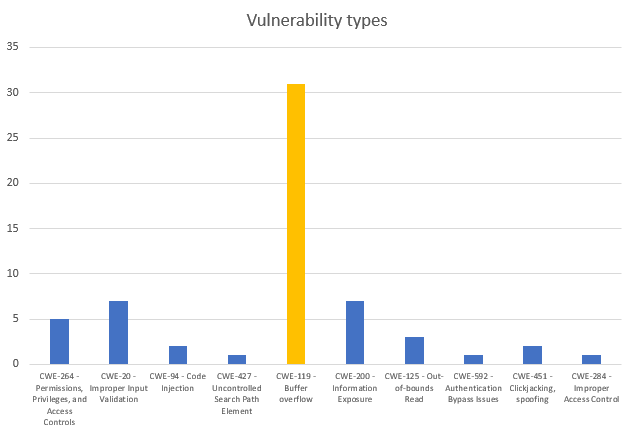
The majority of weaknesses, as usual, are buffer errors (34), the second place is divided between information exposure and input validation errors (7 for each). 5 vulnerabilities are related to improper permissions management.
Zero-days
Microsoft has patched two vulnerabilities that are being exploited in the wild in limited targeted attacks.
Vulnerability in Windows Shell (CVE-2018-8414) is related to path validation and allows a remote attacker to execute commands via a specially crafted file.
Another zero-day in Internet Explorer (CVE-2018-8373) is a classic memory corruption vulnerability.
So far there are no additional information about real-world attacks that involved these vulnerabilities.
RCE in Exchange again
Another RCE vulnerability was patched this month in Microsoft Exchange. According to vendor, the vulnerability can be exploited with a malicious email message sent to affected system.
The last memory corruption vulnerability in Exchange was patched in May this year.
RCE in LNK files
And yet again good old Windows shortcuts are under investigation. The wormable bugs are described with two CVEs CVE-2018-8345 and CVE-2018-8346 that allow to abuse Windows Explorer autoplay functionality. The vulnerability can be exploited remotely and was rated by our team with high severity rating.
RCE in Microsoft SQL Server
And last but not least – memory corruption in SQL server. The vulnerability by itself requires that the attacker is able to execute SQL query. However, SQL servers are often used as backend for web applications. If you are running a web application that is vulnerability to SQL injection attacks, then exploitation of this bug gets easier.
Below is a summarized table of this patch Tuesday:
| Software | Severity | CVE/CVSS | Known exploits |
| SB2018081437: Privilege escalation in Diagnostic Hub Standard Collector for Microsoft Windows (1) | |||
|
Windows Windows Server Visual Studio |
Low |
CVE-2018-0952 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081436: Remote code execution in Microsoft COM for Windows (1) | |||
|
Windows Windows Server |
High |
CVE-2018-8349 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081435: Windows lockscreen bypass in Cortana (1) | |||
|
Windows Windows Server |
Low |
CVE-2018-8253 CVSS:3.0/AV:P/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018081434: Security restrictions bypass in Microsoft Windows Device Guard (2) | |||
|
Windows Windows Server |
Low |
CVE-2018-8204 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:L/E:U/RL:O/RC:C CVE-2018-8200 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:L/E:U/RL:O/RC:C |
Not available |
| SB2018081433: Remote code execution in Microsoft Graphics component (1) | |||
|
Windows Windows Server |
High |
CVE-2018-8344 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081432: Privilege escalation in Microsoft Windows Installer (1) | |||
|
Windows Windows Server |
Low |
CVE-2018-8339 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081431: Privilege escalation in Microsoft Windows NDIS (2) | |||
|
Windows Server Windows |
Low |
CVE-2018-8342 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8343 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081430: Multiple vulnerabilities in Microsoft Windows Kernel (3) | |||
|
Windows Windows Server |
Low |
CVE-2018-8341 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8348 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8347 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081429: Information disclosure in Microsoft Office (1) | |||
|
Microsoft Office Microsoft Word Microsoft SharePoint Server Word Automation Services on Microsoft SharePoint Server Microsoft Office Web Apps Microsoft Excel |
Low |
CVE-2018-8378 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018081428: Privilege escalation in Microsoft Office for Mac (1) | |||
| Microsoft Office for Mac | Low |
CVE-2018-8412 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081427: Remote code execution in Microsoft Windows GDI+ component (1) | |||
|
Windows Server Windows |
High |
CVE-2018-8397 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081426: Information disclosure in Microsoft Windows GDI component (3) | |||
|
Windows Windows Server |
Low |
CVE-2018-8394 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8396 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8398 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018081425: Buffer overflow in Microsoft PowerPoint (1) | |||
|
Microsoft PowerPoint Microsoft Office |
High |
CVE-2018-8376 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081424: Multiple vulnerabilities in Microsoft Excel (3) | |||
|
Microsoft Office for Mac Microsoft Excel Microsoft Office Compatibility Pack Microsoft Office |
High |
CVE-2018-8375 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8379 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8382 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018081423: Privilege escalation in Microsoft Windows DirectX Graphics Kernel (DXGKRNL) driver (4) | |||
|
Windows Windows Server |
Low |
CVE-2018-8400 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8401 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8405 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8406 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081421: Remote buffer overflow in Microsoft SQL Server (1) | |||
| Microsoft SQL Server | Medium |
CVE-2018-8273 CVSS:3.0/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081420: Privilege escalation in Microsoft Windows Win32k (2) | |||
|
Windows Windows Server |
Low |
CVE-2018-8404 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8399 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081419: Remote code execution when processing LNK files in Microsoft Windows (2) | |||
|
Windows Windows Server |
High |
CVE-2018-8345 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8346 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081418: Information disclosure in Microsoft .NET Framework (1) | |||
| Microsoft .NET Framework | Low |
CVE-2018-8360 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018081417: Authentication bypass in Active Directory Federation Services (1) | |||
| Windows Server | Medium |
CVE-2018-8340 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2018081416: Multiple vulnerabilities in Microsoft Internet Explorer (10) | |||
| Microsoft Internet Explorer | High |
CVE-2018-8353 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8389 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8371 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8316 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8403 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8351 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8355 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8385 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8372 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8357 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081415: Multiple vulnerabilities in Microsoft Chakracore (9) | |||
| ChakraCore | High |
CVE-2018-8384 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8359 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8381 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8380 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8266 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8355 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8390 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8385 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8372 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081414: Multiple vulnerabilities in Microsoft Edge (16) | |||
| Microsoft Edge | High |
CVE-2018-8377 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8387 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8370 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8358 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:L/E:U/RL:O/RC:C CVE-2018-8388 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8383 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8381 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8380 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8266 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8355 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8390 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8385 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8372 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8403 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8351 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C CVE-2018-8357 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2018081413: Remote code execution in Microsoft Internet Explorer (1) | |||
| Microsoft Internet Explorer | Сritical |
CVE-2018-8373 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:H/RL:O/RC:C |
This vulnerability is being exploited in the wild. |
| SB2018081412: Remote command execution in Windows Shell on Microsoft Windows 10 and 2016 (1) | |||
|
Windows Windows Server |
Сritical |
CVE-2018-8414 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:H/RL:O/RC:C |
This vulnerability is being exploited in the wild. |
| SB2018081411: Multiple vulnerabilities in Microsoft Exchange (2) | |||
| Microsoft Exchange Server | High |
CVE-2018-8302 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2018-8374 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:L/E:U/RL:O/RC:C |
Not available |
| SB2018081410: Buffer overflow in Windows PDF library (1) | |||
|
Windows Windows Server |
High |
CVE-2018-8350 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |