In May 2020 Microsoft has patched 111 vulnerabilities making. This is the biggest amount of issues patched within a single patch cycle this year.
The majority of issues are boundary errors (69 in total), 15 vulnerabilities exist due to incorrect management of permissions and 13 bugs are caused by incorrect input validation.
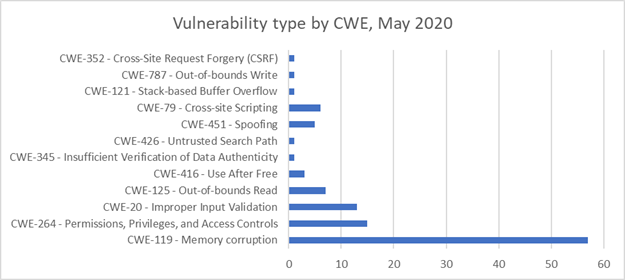
Diagram 1. Vulnerability distribution in Microsoft products by types, May 2020
The majority of bugs have low severity level, however 19 vulnerabilities allow remote code execution and are scored as high.
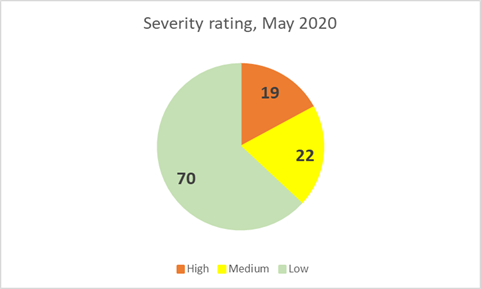
Diagram 2. Vulnerability distribution in Microsoft products by severity rating, May 2020
Almost half of all vulnerabilities can be exploited remotely via Internet or local network (49). 61 vulnerability can be exploited locally and 1 issue requires physical access to the system.
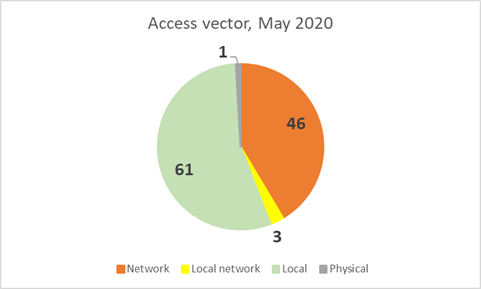
Diagram 3. Vulnerability distribution in Microsoft products by access vector, May 2020
Below is a compiled list of all released bulletins and brief description of published issues:
| Software | Severity | CVE/CVSS | Known exploits |
| SB2020051272: Privilege escalation in Microsoft Windows (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1079 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051271: Denial of service in Microsoft Windows (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1076 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051270: Privilege escalation in Windows Media Service (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1068 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051269: Privilege escalation in Windows Block Level Backup Engine Service (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1010 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051268: Denial of service in Microsoft Windows Transport Layer Security (1) | |||
|
Windows Windows Server |
High |
CVE-2020-1118 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:N/I:N/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051267: Privilege escalation in Microsoft Windows DirectX (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1140 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051266: Privilege escalation in Microsoft Windows Common Log File System Driver (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1154 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051265: Information disclosure in Windows Subsystem for Linux (1) | |||
|
Windows Windows Server |
Medium |
CVE-2020-1075 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051264: Privilege escalation in Microsoft Windows Remote Access Common Dialog (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1071 CVSS:3.0/AV:P/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051263: Privilege escalation in Microsoft Windows Storage Service (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1138 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051262: Remote code execution in Microsoft Windows (1) | |||
|
Windows Windows Server |
Medium |
CVE-2020-1067 CVSS:3.0/AV:A/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051261: Privilege escalation in Microsoft Windows Push Notification Service (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1137 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051260: Remote code execution in Microsoft Color Management Module (ICM32.dll) (1) | |||
|
Windows Windows Server |
High |
CVE-2020-1117 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051259: Privilege escalation in Windows Background Intelligent Transfer Service (1) | |||
|
Windows Windows Server |
High |
CVE-2020-1112 CVSS:3.0/AV:A/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051258: Privilege escalation in Microsoft Windows Graphics Component (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1135 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051257: Remote code execution in Microsoft Graphics Components (1) | |||
|
Windows Windows Server |
High |
CVE-2020-1153 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051256: Remote code execution in Windows Task Scheduler (1) | |||
|
Windows Windows Server |
Medium |
CVE-2020-1113 CVSS:3.0/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051255: Multiple vulnerabilities in Microsoft Connected User Experiences and Telemetry Service (2) | |||
|
Windows Windows Server |
Low |
CVE-2020-1084 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C CVE-2020-1123 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051254: Privilege escalation in Windows Printer Service (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1081 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051253: Privilege escalation in Windows Print Spooler (2) | |||
|
Windows Windows Server |
Low |
CVE-2020-1048 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1070 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051252: Information disclosure in Microsoft Windows Client Server Run-Time Subsystem (CSRSS) (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1116 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051251: Remote code execution in Microsoft Script Runtime (1) | |||
|
Windows Windows Server |
Medium |
CVE-2020-1061 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051250: Privilege escalation in Windows Update Stack (2) | |||
|
Windows Windows Server |
Low |
CVE-2020-1110 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1109 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051249: Remote code execution in Microsoft Excel (1) | |||
|
Microsoft Office Microsoft Excel Microsoft Office for Mac |
High |
CVE-2020-0901 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051248: Remote code execution in Microsoft MSHTML Engine (1) | |||
| Microsoft Internet Explorer | Medium |
CVE-2020-1064 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051247: Remote code execution in Microsoft Chakra Scripting Engine (1) | |||
|
ChakraCore Microsoft Edge |
High |
CVE-2020-1037 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051246: Remote code execution in Microsoft ChakraCore scripting engine (1) | |||
|
ChakraCore Microsoft Edge |
Medium |
CVE-2020-1065 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051245: Spoofing attack in Microsoft Power BI Report Server (1) | |||
| Power BI Report Server | Medium |
CVE-2020-1173 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051244: Denial of service in Microsoft ASP.NET Core (1) | |||
|
Visual Studio ASP.NET Core MVC |
Medium |
CVE-2020-1161 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051243: Denial of service in Microsoft Windows Hyper-V (1) | |||
|
Windows Windows Server |
Medium |
CVE-2020-0909 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051242: Cross-site scripting in Microsoft Active Directory Federation Services (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1055 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051241: Cross-site scripting in Microsoft Dynamics 365 (On-Premise) (1) | |||
| Microsoft Dynamics 365 | Low |
CVE-2020-1063 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051240: Denial of service in Microsoft .NET Core and .NET Framework (1) | |||
|
ASP.NET Core MVC Visual Studio Microsoft .NET Framework |
Medium |
CVE-2020-1108 CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051238: Privilege escalation in Microsoft .NET Framework (1) | |||
| Microsoft .NET Framework | Low |
CVE-2020-1066 CVSS:3.0/AV:L/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051237: Privilege escalation in Microsoft Windows Installer (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1078 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051236: Multiple vulnerabilities in Microsoft Win32k (2) | |||
|
Windows Windows Server |
Low |
CVE-2020-1054 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1143 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051235: Multiple vulnerabilities in Microsoft Internet Explorer (2) | |||
| Microsoft Internet Explorer | High |
CVE-2020-1062 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1092 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051234: Privilege escalation in Microsoft Windows Error Reporting Manager (1) | |||
|
Windows Windows Server |
Low |
CVE-2020-1132 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051233: Multiple vulnerabilities in Microsoft Windows Error Reporting (WER) (3) | |||
|
Windows Windows Server |
Low |
CVE-2020-1021 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1082 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1088 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051232: Multiple vulnerabilities in MIcrosoft Visual Studio Code Python Extension (2) | |||
| Visual Studio Code Python Extension | High |
CVE-2020-1192 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1171 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051231: Multiple vulnerabilities in Microsoft Windows Kernel (3) | |||
|
Windows Windows Server |
Low |
CVE-2020-1114 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1072 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2020-1087 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051230: Remote code execution in Microsoft Edge PDF Reader (1) | |||
| Microsoft Edge | High |
CVE-2020-1096 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051229: Multiple vulnerabilities in Microsoft Edge (2) | |||
| Microsoft Edge | Medium |
CVE-2020-1059 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1056 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051228: Multiple vulnerabilities in Microsoft Media Foundation (4) | |||
|
Windows Windows Server |
High |
CVE-2020-1028 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1126 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1150 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1136 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051227: Multiple vulnerabilities in Microsoft Jet Database Engine (4) | |||
|
Windows Windows Server |
High |
CVE-2020-1175 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1051 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1174 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1176 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051226: Multiple vulnerabilities in Microsoft Windows Clipboard Service (4) | |||
|
Windows Windows Server |
Low |
CVE-2020-1111 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1121 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1165 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1166 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051225: Multiple vulnerabilities in Microsoft Windows GDI (5) | |||
|
Windows Windows Server |
Low |
CVE-2020-0963 CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2020-1179 CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2020-1141 CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2020-1142 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1145 CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051224: Multiple vulnerabilities in Microsoft Windows State Repository Service (12) | |||
|
Windows Windows Server |
Low |
CVE-2020-1191 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1188 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1187 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1185 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1184 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1131 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C CVE-2020-1190 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1189 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1186 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1144 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1134 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1124 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051223: Multiple vulnerabilities in Microsoft Windows Runtime (12) | |||
|
Windows Windows Server |
Low |
CVE-2020-1164 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1139 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1125 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1090 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1086 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1077 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1158 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1157 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1156 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1155 CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1151 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1149 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051222: Multiple vulnerabilities in Microsoft VBScript (4) | |||
| Microsoft Internet Explorer | Medium |
CVE-2020-1035 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1058 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1060 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1093 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |
| SB2020051220: Multiple vulnerabilities in Microsoft Office SharePoint (4) | |||
|
Microsoft SharePoint Server Microsoft SharePoint Foundation |
Low |
CVE-2020-1099 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1101 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1100 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1106 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C |
Not available |
| SB2020051219: Multiple vulnerabilities in Microsoft SharePoint (8) | |||
|
Microsoft SharePoint Server Microsoft SharePoint Foundation |
Medium |
CVE-2020-1105 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1104 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1103 CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1102 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1069 CVSS:3.0/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1107 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:N/E:U/RL:O/RC:C CVE-2020-1024 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C CVE-2020-1023 CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C |
Not available |